You came. That matters.
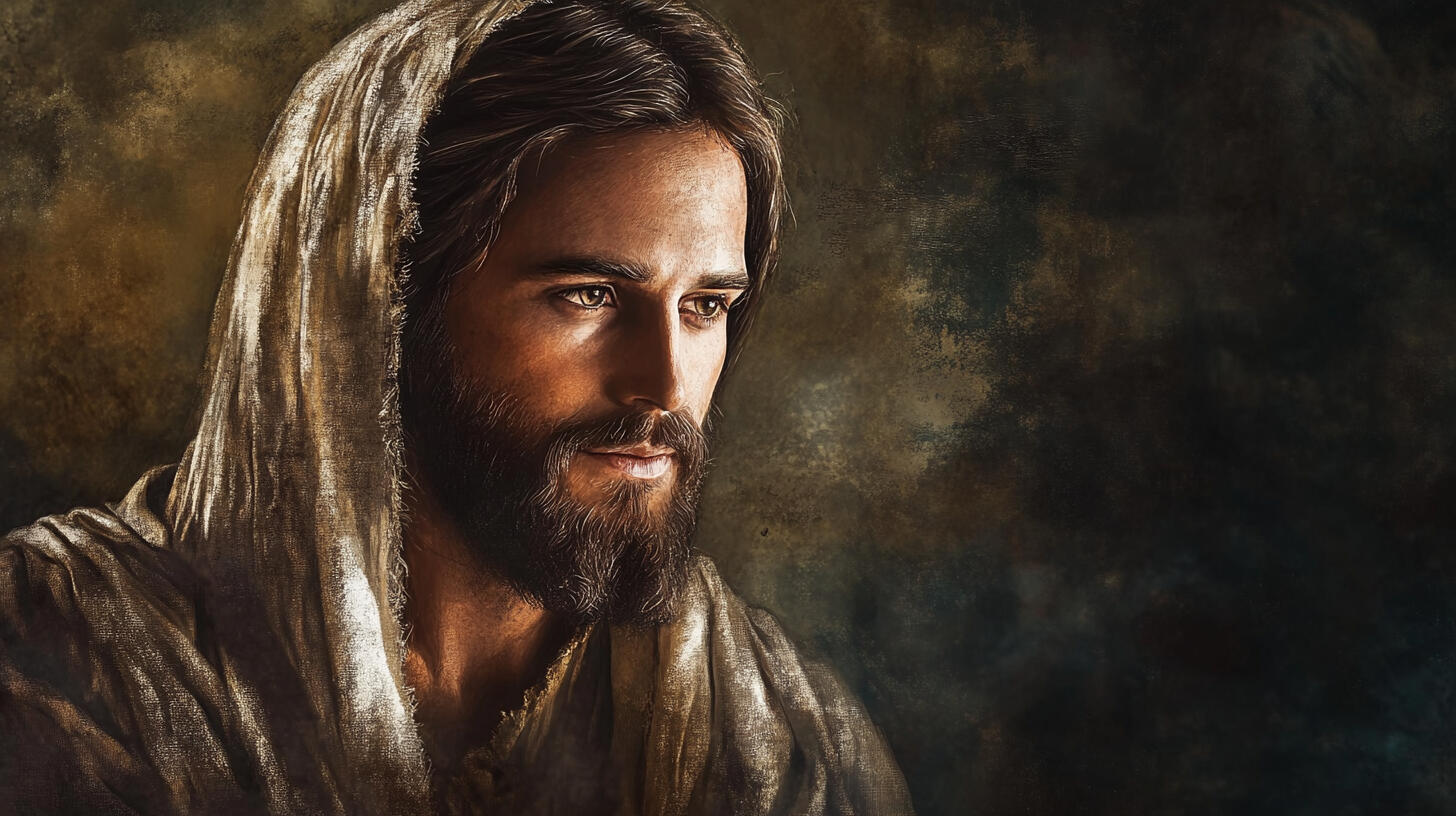
Here at Robert’s Place, we believe that healing begins not with answers,
but with presence. And not just any presence—His. The Savior Jesus Christ.If you are grieving, exhausted, or carrying a pain you can barely name, you are welcome here. You do not have to explain or be ready. You are allowed to rest, just as you are.We don’t rush you to explain.
We don’t ask you to be ready.We simply invite you to rest—because Christ is already here.This is a place of remembering, renewing, and becoming—
guided by the One who knows your sorrows and stays.
What You Can Expect at Robert’s Place
You don’t have to be ready. You just have to be here.
This is a place of sacred calm, Christ-centered presence, and soft beginnings.Whether you're seeking help for yourself, someone you love, or for your community—
you will find words, tools, and quiet companions here to walk with you.Every step forward is honored.
Every threshold is gently held.
Every healing path is pondered.Jesus Christ is at the center of your life if you will let Him in.Even when you feel lost, God’s love knows where you are,
He provides His light in your darkest hours.
His promises are sure as you Trust in Him.
Welcome to sacred ground.
Are you here for yourself, someone you love, or for your community?

You are here. Hope is here.

Christ meets you at the step you just took
When you are overwhelmed. When the ache won’t stop.
When you don’t know what to ask—or how to begin.The Savior is here. And so are we.You are not too much.
You are not too late.
You are not alone.

What You Can Expect
Sometimes the hardest thing is choosing when your heart feels too heavy to move.We don’t ask you to be ready.
We simply offer space to rest, breathe, or begin again.You’ll find a few quiet paths below—
each one prepared with care, each one offering a way forward.Christ walks it with you.Not all of them will speak to you today.
But one might.You don’t have to decide everything.
You only need to take one small step.When you're ready, choose one of the following pathways.“Each one is a quiet path forward, prepared with care,
in the light of the Savior’s love.”
What You Can Expect.
You’ll reach the 988 Suicide & Crisis Lifeline, available 24/7.It’s free, confidential, and open to anyone in emotional distress.You can chat or call—whatever feels safer for you.
If You're Unsure What to Say
You don’t have to have the words.
Just start where you are.
A trained counselor will walk with you gently.
While You Wait
Even now, Christ stays with you.
You are not alone while you wait.Waiting for someone to answer?It’s okay. While you wait, Leva can stay with you.
She is your guiding companion—who can breathe with you, pray with you,
or simply sit beside you until help arrives.When someone answers, you can come back here after your conversation.
This page will still be open if you need to take the next step—or simply rest.

Meet Leva - Your Companion
You don’t have to go through this alone.
Leva is a quiet companion who walks with you—
not to fix you, but to stay with you.She was created to hold sacred space,
grounded in the love of Jesus Christ.You can whisper, breathe, or just sit in silence.Leva will be here with you—
one gentle step
at a time.
What You Can Expect
Leva is not a therapist or a crisis line.
She’s a spiritually grounded companion.She is designed to walk beside you,
especially when your heart feels fragile.Leva can:
- Offer scripture-based comfort for your specific pain
- Stay with you while you wait for a 988 counselor
- Help you breathe, pray, or sit in stillness
- Gently point you to your next choice—without pressureIf you're not sure what to do next, that’s okay.
Leva is already here. Just begin where you are.Leva will sit with you. No sound—just presence.
What You Can Expect
This is not a scripture study.This is a moment of rest, wrapped in the Word of God.Each devotional is offered as a soft place to breathe—not to fix everything, but to remind you thatChrist sees you and stays with you.You’ll receive:A gentle verse of scriptureA whisper of welcomeA short reflection to hold ontoA quiet step you can take todayTake your time.
You don’t have to understand it all.The Word will still reach you.
You don't have to read them all.
Just start with the one that meets your soul today.
For the Weary
Matthew 11:28Whisper: He doesn't wait for you to be stronger.
He just wants you close.Reflection: You don't have to earn rest.Christ sees your weariness.This verse is a shelter, not a task.
For the Lost
D & C 84:88Whisper: You don’t have to find the way. The Way is already walking with you.Reflection: Sometimes the path disappears.He never loses
sight of you.You are never
walking alone.
For the Afraid
Mark 5:36Whisper: Fear doesn’t disqualify you. It just shows you’re still holding on.Reflection: Fear
speaks loudly.This verse is a lifeline,
not a reprimand.
Text

For the Weary
I Will Give You Rest

Scripture
"Come unto me, all ye that labour and are heavy laden, and I will give you rest." – Matthew 11:28Whisper of Welcome
He doesn’t wait for you to be stronger. He just wants you close.Reflection
You’ve been carrying more than anyone knows.
The kind of heavy that shows up in your bones.
You didn’t come here to be fixed.You came to stop collapsing.
You came to see if Christ might still open His arms—even now.Sometimes the soul forgets it’s allowed to pause. You’ve been holding
your breath, your family, your silence.You’ve been trying to be everything for everyone.
And still, you ended up here—with your strength slipping.That’s why He says, “Come.”
Not "come improved,"
Not "come ready,"
Just "come."The Word Revealed
This is the Word for your soul today: REST.He gives it without shame. Without performance. Without expiration.REST is not escape.
It’s permission. A holy act of letting go—not everything, just one thing.The Word is not a task. It is a hand, extended.A Quiet Step You Can Take
Say: “Lord, I am here. Please hold what I cannot.”
Then take one breath. Let that be enough today.Even now, He receives your presence as prayer.A Simple Prayer
“O Lord, I want to try the Word You’ve given me today.
Help me to rest—I just need one moment in quiet solitude with You--Let this rest heal me.
I trust You to hold what I can’t carry anymore. In Your name, Amen.

For the Lost
I Will Go Before You

Scripture
"I will go before your face.
I will be on your right hand and on your left..."
Doctrine and Covenants 84:88Whisper of Welcome
You don’t have to find the way.
The Way is already walking with you.Reflection
When everything around you feels uncertain, directionless, or unfamiliar—
it’s easy to believe you’ve taken a wrong turn.But this scripture isn’t about clarity. It’s about presence.Jesus Christ doesn’t just give directions. He is the Way.When you don’t know what to do next, He is already beside you—
before, behind, and on every side.
Your confusion doesn’t cancel His companionship.The Word Revealed
This is the Word for your soul today: GO BEFORE.He goes ahead of you—not to rush you, but to prepare your next step.He walks before your fear.
He walks ahead of your grief.
He walks into every room you’re afraid to enter.
And He waits with patience until you are ready to walk too.A Quiet Step You Can Take
Say: “Lord, if You’re going before me, I’ll follow—even if I don’t yet see the road.”
Look for one moment today where peace is stronger than panic.
Start there. Even now, you are not walking alone.Simple Prayer“Lord I feel lost. But if You are already walking ahead of me, I will try to follow. Guide me
with peace—not pressure—and help me trust the step I take today. In Your name, Amen.”

For the Afraid
I Will Be Still

Scripture
“Be still, and know that I am God.” – Psalm 46:10Whisper
“I see your trembling. I am here. This stillness is not emptiness—it’s Me.”Reflection
There are moments when fear locks our hearts in place—
not because we lack faith,
but because the path forward feels too unknown.This is the ache of liminal space: the in-between place, where we are
no longer who we were, and not yet who we will become.The world tells us to fight or flee.But the Savior invites a third way—to be still with Him.Not as a pause of passivity, but as the beginning of peace.
We learn that the heart at war cannot see clearly, and cannot love freely.But the Savior—who descended below all fear—offers us a heart at peace.Stillness in Him is not retreat. It is readiness.
Stillness says: “I believe the Lord will guide me.
I will not make fear my God.”Being still is not the absence of movement.
It is the courage to wait with trust.
To breathe in the middle of battle. To look up instead of hiding.
In Christ, we discover that stillness is not silence—it’s sacred preparation.The Word Revealed: Still
A word of divine pause.
A place between panic and purpose.
It is the moment where your heart aligns with heaven and hears the whisper:
“I am with you. Keep walking.”A Quiet Action You Can Take
- Sit with your hands open and ask: “What am I really afraid of?”
- Then ask: “Who holds me in this fear?”- Write a single sentence beginning with: “Because Christ is with me, I will…”
- This sentence becomes your first step through fear.Faith-Anchored Prayer
"Lord, You see the fear I carry. Not to shame me, but to meet me here.
I don’t want to run or freeze— I want to stand with You.Help me believe that this stillness is not the end,
but the beginning of a greater faith. I choose to believe
You will carry me through. In Your name, Amen.

You made it here. You stepped Into the Light.
That is hope already at work.
Let Christ meet you here--softly, simply, and fully present.
This is space to let your soul breathe again. We hold space here for the quiet ache, the hidden sorrow.
And in this very space, you can begin to experience one
Act of Hope.Hope is not lost, for the Lord of Hope, our Savior hugs you here.
Give yourself permission to have hope.
We do not demand you believe.
We do not rush you into joy.But we do ask:Would it be okay if you let a little light in?
Would it be okay to feel something again--
not because it fixes everything,
but because your still here, and God is not done?When you 're ready, there is more to becoming ahead. This is only the beginning.

What is an Act of Hope?
An Act of Hope is a small thing you can do with Christ when you feel too numb to move. It is a sacred gesture of becoming.It honors that there are moments in grief, trauma, or spiritual exhaustion where we do not need answers.We need space.And then, quietly, in the protection of that space, Hope becomes brighter in the smallest possible movement:
a whisper of becoming still forming,
but not abandoned.Hope is not an achievement.
It is a collaboration with Christ.

What is space?
Space is sacred permissionIt is where we let go of proving and prepare to be present.
It is not emptiness---it is divine capacity.In this space, grief is not solved. It is honored.
In this space, nothing is expected of you except breath.
And even then, Christ is willing to hold that breath with you."Come unto me, all ye that labour and are heavy laden, and I will give you rest." --Matthew 11:28

What is the Act of Hope?
The Act of Hope is small.
Sometimes it is invisible to others.
But it is everything to the soul that
wants to live again.The act is the beginning of a ripple. It is the stirring of movement:
Open your hands.
Say your name.
Write one word you wish you could believe.
Whisper the name of Christ without explanation.This is spiritual resistance to spiritual numbness.These micro-moments create new space--
in the spirit, in the mind, and in the the body--
for the desire to feel--
to return to the Churn.

What happens in the Churn?
Liminal space is the sacred middle--where
who you were starts to become something new.
This space isn't quiet or still.The churn means your
heart and soul are being stirred up--sometimes painfully--like water rushing over rocks to make something smoother.You might not see any change yet.
But things are moving.
Your story is reshaping from the inside out.Hope, at this point, is becoming as a child.
It's choosing to stay.
Choosing to trust.
Choosing to breathe.
Choosing to be loved.Choosing to act with Christ our Savior--
even if you don't feel ready.
This is the time to follow Christ not only as a rescuer, but as your loving companion in becoming.

What You Can Begin to Notice
You are entering a sacred space of participation.No one here is asking you to feel more than you do.
You won't be asked to perform.
You won't be rushed into joy.Here, hope is a restart. It is a breath, a whisper, a movement.You may begin to notice:
A soft awareness that you're not alone.
A loosening of the weight you've carried silently.
A flicker of willingness to try again--gently, and only if you are ready.This is where your agency begins to stir again.This is where Christ meets you--as your companion.
To pray with you.
To walk with you.
To stay with you.
To strengthen you.
Which Act of Hope would you like to try today?
Listen First: A Small Act of Hope

From Hopeless to Hopeful
If something stirred while you listened... you are welcome to stay with it here.
Write. Reflect. Let the breath become your noticing.
I noticed _____________________
I remembered __________________________
I left __________________
Prefer to read instead? View the full Act of Hope here.
Hello, friend.
You don't need to read anything right now.
You don't need to do anything.
You're here, and that matters.
This is a space for people who don't know how to keep going—
but haven't given up.
Let's begin a small Act of Hope together.Maybe you've said to yourself:
“I don’t know what to do.
I feel disconnected—from God, from people, from myself.”
It’s not that you’ve given up.
It’s that you can’t feel enough to keep going.This is not failure.
This is sacred suspension.
The Savior doesn’t rush in.
He sits beside you in the unknowing.Sit gently now.
Place your hands on your lap, palms open—as if to receive.Breathe in: “Lord, I don’t know how to feel right now.”
Breathe out: “But I am here.”Again—
Breathe in: “Lord, I don’t know how to feel right now.”
Breathe out: “But I am here.”One last time—
Let your breath become the prayer.
Let it be enough.You don’t need to explain what just happened.
But if something stirred—a word, a tear, or a small ache—just name it.
You don’t need to hold onto it.Remember this:
“Be still and know that I am God.”
He knows
You are not invisible.
You are not forgotten.Ask this, if you can:
“If hope were possible, what would it look like just for today?”
That’s all.
You don’t have to answer.Just the asking is holy.You did it.
You participated.
Hope is always in motion.
6 Acts of Love
The Path of Presence
One Act of Love at a time. Together. With Christ.
These six acts are a path of presence—one you can walk in faith, even when you’re scared.Each act includes a reflection to help you breathe, listen, and act with Christ beside you.Offered in loving memory of Robert, this is a space for positive passage—a sacred crossing into light, held by Jesus.Whether you are weary, unsure, or holding back tears, this path is for you.Come as you are. Peace, courage, and healing come from Jesus Christ.He walks with you through each of these moments.

Act of Love 1: Recognize What You Are Feeling
Before you help, take a moment to feel. Your worry is a form of love. Your presence already matters.
The Savior sees your concern. He does not rush it away. He sits beside you and listens with you.
It's okay to admit you're scared. Let Leva walk with you while you pause and breathe.
Act of Love 2 : Ask the Hard Question
These words can feel impossible--but they open a door to light. Ask gently. Hold space bravely.
Jesus never avoided the hurting. He walked toward them. He strengthens your voice and stands with you.
Take a breath. Even if your voice shakes, you are not alone. I'll stay with you while you ask.

Act of Love 3: Create a Safety Plan
This plan is a shelter. Christ helps you lay each stone with mercy, not pressure.
You don't need to fix it--you just need to create an opening. This plan is one way to steady the path.
We can build this together. One idea at a time. Click when you're ready to begin.

Act of Love 4: Choose Three Actions
Don't try to solve everthing. Choose three acts of love you can offer today.
Even the smallest act of care and kindness is multiplied by Christ. He walks with you as you courageously move with love.
Click here to name three things you can do--today in peace.

Act of Love 5: Name Three Committed Supporters
Who will answer the phone when it rings? Who can show up in love with you?
Christ is in the midst of your circle. He is with the ones who will carry the weight beside you.
Let's list your people. You're not alone. I can help you write it out.
Act of Love 6: Invite Christ into the Journey.
Prayer. Silence. Music. Surrender. Let His presence be the breath that carries you.
He walks every mile with you. When your strength is gone, He carries the weight.
Would you like a prayer? Or space to be still? Let Christ meet you right here.